The digital transformation of Human Resources is no longer a future-state aspiration; it is an urgent, operational reality. Mid-sized to enterprise organizations (1,000+ employees) are rapidly deploying sophisticated HR Management Systems (HRMS), talent acquisition platforms, and AI-driven engagement tools. However, this sprint toward digital agility has inadvertently triggered a massive cybersecurity and compliance vulnerability. When HR leaders bypass IT to purchase user-friendly software, and IT responds by locking down systems to the point of friction, the enterprise is caught in a dangerous tug-of-war.
This resulting friction creates “feature-led chaos”—a state where tools are bought to solve symptoms while the underlying architectural disease of fragmented, unsecure data remains untreated. At Mainstay People Consulting, we operate as your Enterprise Enabler. We combine the deep, analytical wisdom of the Sage with the proactive, results-driven execution of the Hero. We recognize that true enterprise transformation requires bridging human capital strategy with cutting-edge platforms, and that bridge must be built on a foundation of uncompromising security.
This Middle-of-Funnel (MOFU) Pillar Playbook is designed for CHROs, Chief Information Security Officers (CISOs), and Compliance Directors who are tired of the friction between HR agility and IT security. Here, we decode how to implement Security-by-Design and establish practical rules for people data governance that scale with your enterprise.
1. The Modern Threat Landscape for People Data
Before we can build the governance framework, we must understand the gravity of what we are protecting. “People Data” is no longer just a list of names and employee ID numbers. Modern HR platforms house the most sensitive, concentrated trove of Personally Identifiable Information (PII) in your entire enterprise.
The “Crown Jewels” of Corporate Data
A comprehensive HR platform contains:
- Financial Data: Bank account numbers, compensation history, and stock options.
- Healthcare and Biometric Data: Insurance enrollments, medical leaves, and fingerprint/facial recognition data for attendance.
- Behavioral and Psychometric Data: Performance review narratives, flight-risk predictions, and confidential grievance reports.
For malicious actors, this data is infinitely more valuable on the dark web than basic consumer credit card numbers. Furthermore, the regulatory penalties for mishandling this data—whether through external breaches or internal negligence—are staggering.
The Fallacy of Compliance via Software
The most common mistake enterprise leaders make is assuming that buying a secure software platform automatically makes the enterprise secure. You can purchase the most advanced HRMS on the market, but if an HR manager downloads a CSV file of compensation data to a local, unencrypted hard drive to run a macro, your enterprise is compromised.
This is the “Shadow HR” dilemma. In the absence of a unified, enterprise-grade data strategy, individual managers turn to manual workarounds. According to extensive research on data strategies by Harvard Business Review, organizations that fail to establish strict data governance protocols suffer from operational silos that not only stifle innovation but exponentially increase the risk of regulatory non-compliance. Compliance is not a feature you buy; it is a habit you architect.
2. Security-by-Design: The Sage’s Anchor
At Mainstay, our core philosophy is to be “stable as a banyan tree, agile as a gazelle.” When it comes to compliance and data privacy, your data governance framework is the Banyan tree. It is the deep-rooted Anchor that allows your organization to move with speed and agility.
Security-by-Design means that data privacy and compliance are not retrofitted onto a system just before “Go-Live.” Instead, they are the foundational blueprints drawn before a single tool is configured. As a Sage brand driven by knowledge and truth, we know that features do not drive transformation; architecture does.
Defining the Single Source of Truth
To achieve Security-by-Design, you must first establish a Master Data Management (MDM) strategy. You must unequivocally answer the question: Which system owns this specific piece of data?
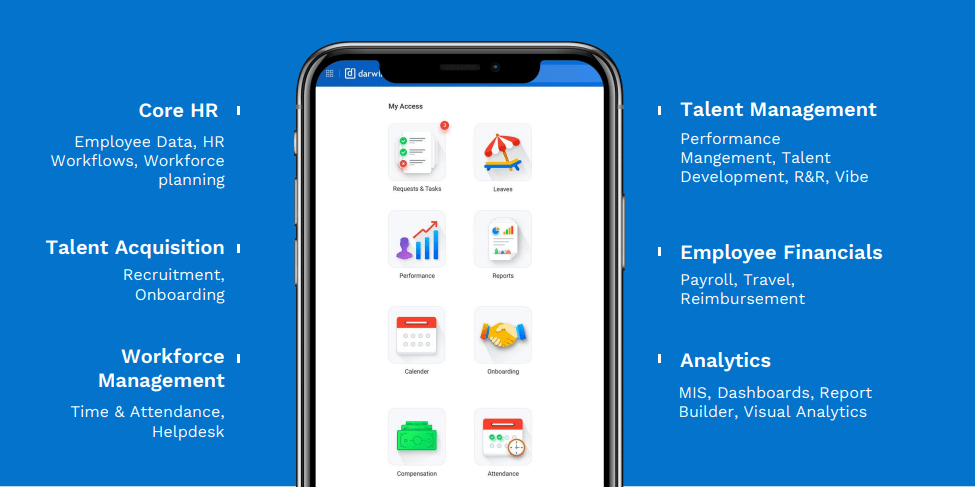
- If Darwinbox is your core HRMS, it must be the sole source of truth for organizational hierarchy and employee lifecycle status.
- If your ERP handles payroll, it must be the sole source of truth for taxation and ledger distribution.
When systems are integrated without a defined Single Source of Truth, data duplicates and fragments. A terminated employee might be removed from the HR platform but remain active in the CRM or ERP, creating a massive security vulnerability. Our “Systems Eye” precision ensures that structural clarity, data logic, and ownership are defined prior to configuration.
3. The 5 Practical Rules for People Data Governance
To operationalize Security-by-Design, enterprises must shift from vague security policies to rigid, executable rules. Here are the five practical rules of people data governance that Mainstay embeds into every transformation project.
Rule 1: Establish Strict Data Contracts (Integrations)
A data contract is a rigid, programmable agreement between systems regarding how data is structured, validated, and transferred. You cannot allow platforms to share data indiscriminately.
- The Rule: No integration shall be built without a documented data contract that specifies the exact fields to be transferred, the encryption standard in transit, and the validation rules required for acceptance.
- The Practice: If your HRMS is pushing data to your financial system, the data contract ensures that sensitive elements like an employee’s home address or demographic data are stripped out of the API payload, as Finance only needs the cost center and salary bandwidth to run forecasting.
Rule 2: Implement Role-Based Access Control (RBAC) and the Principle of Least Privilege
In a 3,000+ employee organization, over-permissioning is a silent killer. Managers often request broad system access “just in case” they need to view a report, leading to widespread visibility into sensitive peer compensation or performance data.
- The Rule: Access to people data is granted strictly based on the user’s role, and defaults to the absolute minimum access required to perform their daily duties (The Principle of Least Privilege).
- The Practice: We architect RBAC matrices that dynamically adjust. If a mid-level manager is temporarily acting as a department head, their access privileges elevate automatically and, crucially, revert automatically when the temporary assignment ends. This eliminates the “access creep” that plagues legacy systems.
Rule 3: Enforce Single Sign-On (SSO) and Automated Lifecycle Provisioning
Password fatigue leads to weak passwords, which leads to compromised networks. Furthermore, manual IT ticketing for onboarding and offboarding is too slow and error-prone for modern enterprises.
- The Rule: All enterprise HR platforms must sit behind a centralized Identity Provider (IdP) requiring Single Sign-On and Multi-Factor Authentication (MFA).
- The Practice: When we manage a large-scale Darwinbox implementation, we tightly couple the HRMS with your Active Directory or Okta environment. When an employee is marked as “Terminated” in HR, the automated workflow revokes their access to every corporate system—email, Slack, CRM, and VPN—within milliseconds. This zero-trust approach mitigates the risk of disgruntled former employees walking away with confidential IP.
Rule 4: Data Residency and Localization Compliance
Global and regional data privacy laws are becoming increasingly stringent. The General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA), and India’s Digital Personal Data Protection (DPDP) Act all place severe restrictions on where people data can be stored and how it can be processed.
- The Rule: Enterprise architecture must map and comply with the geographic data residency requirements of its workforce, ensuring data does not cross borders illegally.
- The Practice: We configure cloud instances that partition data logically and physically based on the employee’s legal jurisdiction. Furthermore, we build automated retention policies. If the law states candidate data must be purged after 12 months of inactivity, the system executes that purge automatically, leaving an audit trail, rather than relying on a recruiter to remember to hit “delete.”
To understand the broader business implications of privacy legislation, insights from McKinsey & Company detail how proactive data privacy strategies are evolving from a purely legal requirement into a distinct competitive advantage for building institutional trust.
Rule 5: Establish Continuous Audit Rhythms
A governance framework is only as effective as the rituals that enforce it. Security is not a “set it and forget it” endeavor; it requires continuous, proactive oversight.
- The Rule: Technical health checks and access audits must be operationalized into regular, automated governance rhythms.
- The Practice: Our Application Managed Services (AMS) teams do not just fix broken APIs; we conduct quarterly access audits. We provide CISOs with dashboards that highlight “dormant accounts” or “privilege anomalies,” allowing security teams to intervene before a breach occurs. We adhere strictly to recognized frameworks; as defined by Gartner, data governance is the specification of decision rights and an accountability framework to ensure the appropriate behavior in the valuation, creation, consumption, and control of data and analytics.
4. Bridging the CHRO and CTO Divide
The greatest barrier to implementing these five rules is not technical; it is cultural. In many enterprises, the CHRO and the CTO operate in adversarial silos. The CHRO wants a platform that offers a beautiful, frictionless employee experience. The CTO wants a platform that is locked down, risk-averse, and compliant.
When these leaders clash, transformation stalls. The “Siloed Struggle” results in technology decisions that fail to address the actual daily workflows of the workforce while simultaneously opening up shadow-IT vulnerabilities.
The Enterprise Enabler as the Bridge
At Mainstay, we act as the bridge between human capital strategy and technical architecture. Our persona is uniquely equipped to speak both languages.
- To the CHRO: We are the empathetic problem-solvers (the “Human Handshake”) who understand that if a system is too hard to log into, adoption will fail. We design “Path of Least Resistance” workflows where the secure way to work is also the easiest way to work.
- To the CTO: We are the architectural authority (the Sage). We bring the precision expertise necessary to speak about API payloads, encryption-at-rest, and SOC compliance. We do not brush off security concerns to make a quick sale.
By forcing cross-functional alignment, we ensure that the HR system is not viewed as an “HR tool,” but as an enterprise-grade digital enabler.
5. The New Frontier: AI and People Data Governance
The introduction of Artificial Intelligence into HR operations has exponentially increased the complexity of data governance. Enterprises are eager to deploy AI to predict turnover, automate document generation, and power employee service chatbots. However, AI introduces two massive risks: Data Poisoning and Algorithmic Hallucination.
Preventing Data Poisoning
Generative AI and Large Language Models (LLMs) are only as intelligent as the data they consume. If your HR data is fragmented, biased, or inaccurate, the AI will confidently generate biased and inaccurate outputs. This is why our “Anchor” of Master Data Management must precede any AI “Thrust.”
Before we integrate advanced tools to enable AI-powered query resolution or workflow automation, we ensure the data lake feeding that AI is sanitized, validated, and tightly governed.
Controlling Hallucinations with RAG
To prevent an HR chatbot from hallucinating an incorrect answer regarding a sensitive medical leave policy, we utilize Retrieval-Augmented Generation (RAG) architectures. This ensures the AI is not “thinking” on its own; it is strictly retrieving answers from your pre-approved, legally vetted corporate policy documents.
Furthermore, the RBAC rules discussed in Rule 2 must apply to the AI. If an employee asks the AI, “What is the CEO’s bonus structure?”, the AI must recognize the user’s permission level and refuse the query based on established governance guardrails.
6. Measuring Governance Success: Leading vs. Lagging Indicators
How do you know if your people data governance strategy is actually working? Most organizations rely on a lagging indicator: Did we get breached or audited this year? If the answer is no, they assume the strategy is working.
As an outcome-obsessed firm, we believe in tracking leading indicators—metrics that prove your governance is actively preventing risk.
Leading Indicators for Data Governance:
- Orphaned Account Rate: The percentage of active system accounts belonging to employees who have left the company. In a governed system with automated SSO de-provisioning, this number should be exactly zero.
- Access Escalation Frequency: How often are employees requesting emergency access to data outside their standard RBAC profile? A high frequency indicates that the original role design is flawed and needs architectural adjustment.
- Data Sync Error Rate: The number of validation failures occurring across your API data contracts. A dropping error rate proves that your Master Data Management rules are successfully maintaining a Single Source of Truth.
By building executive dashboards that track these leading indicators, we give the CHRO and the CISO the data-driven clarity they need to sleep soundly at night.
7. The Mainstay Advantage: Execution Excellence with Integrity
Designing a governance framework is challenging, but executing it across a 1,000+ employee enterprise requires true “Heroic” drive. Many legacy consulting firms will gladly sell you a 100-page PowerPoint deck outlining your theoretical governance risks, but they disappear when it is time to actually configure the APIs and build the RBAC matrices.
We do not believe in hit-and-run consulting. We bring the focus, depth, and speed of a specialized firm, combined with the scale and stability to see it through.
- Boutique Attention: You gain direct access to our senior architectural leadership. We act as your trusted advisor, telling the truth—even if it is uncomfortable—about your current security vulnerabilities.
- Enterprise Backbone: We don’t just give advice; we dive in to implement solutions. When a complex legacy data migration hits a snag, our culture is to take ownership, rally the team, and execute a secure workaround without compromising the data contract.
If you want to understand more about how we balance the stability of secure architecture with the speed of modern business, we encourage you to explore our Anchor + Thrust philosophy.
Start Your Secure Transformation
True transformation is not about moving fast and breaking things; it is about moving fast because your foundation is unbreakable. If your enterprise is struggling with shadow HR systems, fragmented data logic, or the paralyzing friction between HR agility and IT compliance, it is time to redesign your operating model.
Mainstay People Consulting bridges strategy and systems to deliver people-led, tech-powered results with uncompromising integrity. We lead with listening, solve with precision, and deliver with speed.
Ready to turn compliance from a roadblock into a competitive advantage?
[Book a Discovery Call] — Speak directly with our technical leadership to audit your current HR architecture, define your data contracts, and build a governance framework that empowers your enterprise to scale securely.